Verification of primitive Sub-Ghz RF replay attack techniques based on visual signal analysis | Semantic Scholar

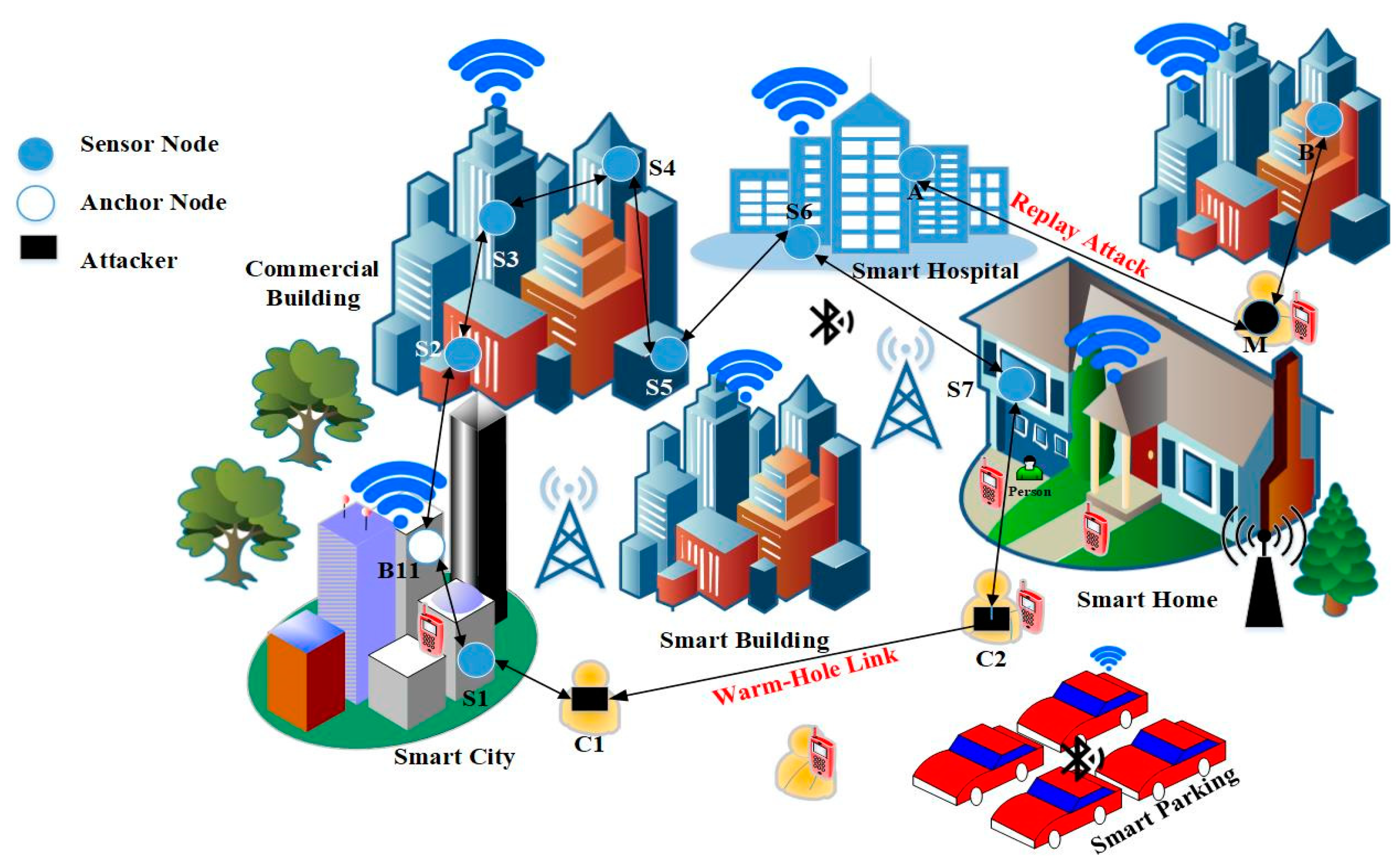
Securing a wireless sensor network for human tracking: a review of solutions - Carrasco - 2014 - International Journal of Communication Systems - Wiley Online Library

Verification of primitive Sub-Ghz RF replay attack techniques based on visual signal analysis | Semantic Scholar

Verification of primitive Sub-Ghz RF replay attack techniques based on visual signal analysis | Semantic Scholar

Verification of primitive Sub-Ghz RF replay attack techniques based on visual signal analysis | Semantic Scholar

Amazon.com: Whistler TRX-1 Handheld Digital Scanner Radio Black 7.75in. x 7.31in. x 5.75in. : Electronics

Verification of primitive Sub-Ghz RF replay attack techniques based on visual signal analysis | Semantic Scholar

RollBack - A New Time-Agnostic Replay Attack Against the Automotive Remote Keyless Entry Systems - YouTube